Navigating the Evolving Landscape of Digital Identity Trends
Navigating the Evolving Landscape of Digital Identity Trends
Blog Article
The realm of digital identity is in a constant state of flux, driven by rapid technological advancements and evolving user expectations. Consumers are increasingly requiring greater control over their online information, while companies are evolving their strategies to meet these changing requirements. This creates a dynamic landscape where creativity is paramount.
Remaining current of these trends is crucial for both consumers and organizations to thrive in the digital age. Significant developments include the increase of decentralized identity solutions, the melding of artificial intelligence with identity management systems, and the expanding importance of data privacy and security.
- Distributed Ledger Technology
- Secure Authentication Methods
- Facial Recognition
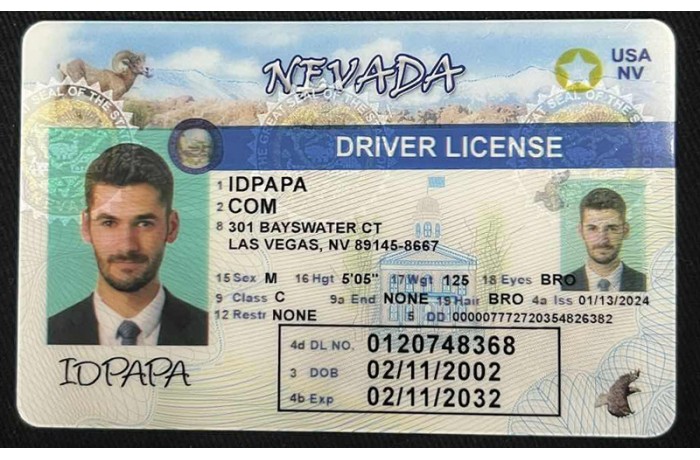
Combatting the Rise of ID Fraud: Strategies for a Secure Future
In today's increasingly digital landscape, identity theft poses a significant threat to individuals and organizations alike. With sophisticated cybercriminals constantly evolving their tactics, combating the rise of ID fraud requires a multi-faceted approach. Robust security measures are essential to protect sensitive personal information. Implementing strong authentication protocols, such as multi-factor verification, can help prevent unauthorized access to accounts. Additionally, raising public consciousness about the dangers of ID fraud is paramount. Individuals should be enabled with the knowledge and tools to safeguard their identities. Promoting data security best practices, including using strong passwords and being cautious regarding phishing scams, can minimize the risk of becoming a victim.
- Furthermore, collaboration between government agencies, financial institutions, and technology companies is key to effectively combat ID fraud.
- Sharing information about emerging threats and adopting industry-wide security standards can strengthen the overall defense against cybercriminals.
By implementing these strategies, we can work towards a more secure future where individuals' identities are protected from detrimental exploitation.
Tightening copyright Laws in the Digital Age
As technology rapidly evolves, so too must our legal frameworks. The rise of complex digital tools has created emerging challenges for combating the creation of fake identification documents. Established laws, often formulated in a pre-digital era, are proving adequate in addressing these modern threats. Regulators must collaborate with experts to formulate cutting-edge solutions that can efficiently combat this expanding problem.
It is vital to confirm that our legal frameworks remain applicable in the face of these evolving technological advancements. Through tightening copyright laws and adopting innovative approaches, we can efficiently protect the integrity of our documents.
Strengthening Digital Defenses with Biometric Authentication
In our increasingly digital world, safeguarding user data has become paramount. Traditional authentication methods, such as passwords and PINs, are increasingly vulnerable to malicious intrusions. Biometric security emerges as a robust solution, leveraging unique behavioral traits to verify identities and mitigate the risk of unauthorized access. By employing technologies like fingerprint scanning, facial recognition, or iris verification, biometric systems provide a higher level of security. These methods are inherently difficult to copyright, making it significantly harder for malicious actors to compromise accounts and steal sensitive information.
Biometric security offers strengths that extend beyond enhanced security. Simplified authentication processes eliminate the need for users to remember complex passwords, reducing hassle. Moreover, biometric systems can instantly verify identities, accelerating access to applications and services.
- Moreover, biometric security is continuously evolving with advancements in machine learning and artificial intelligence, further strengthening its ability to recognize anomalous activities.
- Despite these benefits, it's crucial to address potential challenges associated with biometric data, such as privacy compromises and the potential for abuse.
- Consequently, implementing robust security measures, such as data encryption, is essential to mitigate these risks and ensure the responsible use of biometric technology.
Navigating the Future of Authentication: The Crucial Role of Digital IDs in Achieving Seamless Security
As technology rapidly evolves, authentication/verification/access control methods are constantly undergoing transformation. Digital identities, offering a secure/robust/comprehensive and streamlined/efficient/seamless approach to verifying user credentials, are poised to revolutionize the way we authenticate/identify/validate ourselves in the digital realm. However, striking a balance between convenience/user-friendliness/ease of access and security/protection/safeguarding sensitive information remains paramount.
Implementing digital IDs/electronic identities/online credentials effectively requires careful consideration of various factors, including user acceptance/adoption/engagement, technological infrastructure, and regulatory frameworks. Ensuring that digital identity systems are transparent/accountable/auditable while also remaining user-centric/privacy-focused/data-protected will be crucial for building public trust and fostering widespread implementation/integration/deployment.
- Furthermore/Additionally/Moreover, addressing the potential for fraud/identity theft/cybersecurity threats in digital identity systems is essential. Robust security measures/protective protocols/defense mechanisms must be incorporated to mitigate/prevent/counteract such risks and ensure the integrity of digital identities.
- Ultimately/Concurrently/In essence, the future of authentication lies in embracing a holistic approach that combines the benefits/advantages/opportunities of digital IDs with stringent security protocols. By striking this delicate balance, we can pave the way for a more secure/reliable/trustworthy and convenient/accessible/user-friendly digital world.
Digital Identity Protection: A Multi-Layered Approach to Combating Fraud
In today's online landscape, safeguarding your identity has never been more crucial. Fraudulent schemes are becoming increasingly complex, posing a grave threat to individuals and organizations alike. To effectively combat these risks, a multi-layered approach to digital identity protection is required.
This methodology involves implementing a range of tools at different levels, from individual training to robust defensive systems. Firstly, it's essential to establish strong passwords, enable multi-factor authentication, and frequently update your software. Additionally, be cautious of phishing scams Identity documents security and other social engineering attempts.
Furthermore, organizations must invest in advanced security platforms to detect potential threats and protect sensitive data. This includes implementing intrusion detection systems, firewalls, and encryption standards. By adopting a holistic and multi-layered approach, we can create a more secure digital environment for everyone.
 Report this page
Report this page